

Home > News > Product FAQ > RF Jamming vs GPS Spoofing: What’s the Difference?
In the world of counter-drone technology and electronic warfare, two terms frequently surface in discussions about neutralizing unmanned aerial threats: RF Jamming and GPS Spoofing. While both techniques aim to disrupt a drone’s mission and prevent it from reaching its target, they operate on fundamentally different principles and produce very different results.
For security professionals, facility managers, and defense integrators, understanding the distinction between these two electronic countermeasures is not just a matter of technical semantics—it is critical for choosing the right defense strategy, managing legal liability, and predicting the drone’s behavior after engagement.
This article breaks down the mechanisms, effects, and tactical applications of RF Jamming versus GPS Spoofing.
RF Jamming is an electronic attack that overwhelms a receiver with high-power radio noise on a specific frequency band. Think of it as trying to have a quiet conversation in a room while a heavy metal band plays at full volume next to you. You cannot hear the person speaking because the noise floor is simply too high.
In the context of drones, RF jamming typically targets one of two links:
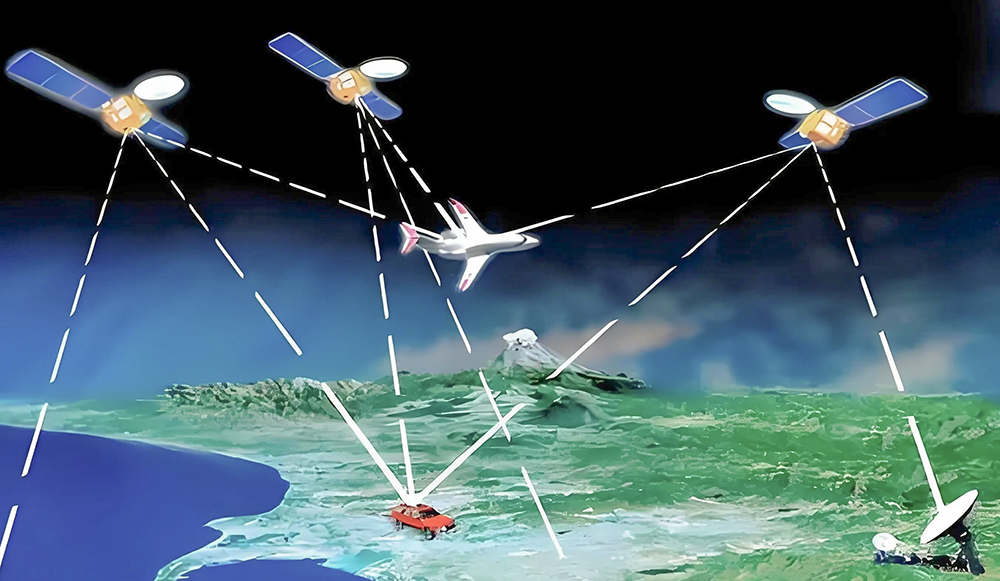
Control Link (2.4 GHz / 5.8 GHz): Jamming this frequency severs the connection between the drone and the pilot’s remote controller.
Navigation Link (GPS L1/L2 / GNSS): Jamming this frequency blinds the drone’s ability to know where it is.
How the Drone Reacts to RF Jamming:
Because RF jamming simply cuts the signal entirely, the drone’s internal safety logic takes over. The drone will enter a failsafe mode defined by its manufacturer. In 95% of commercial drones, this means:
Return-to-Home (RTH): The drone ascends to a safe altitude and flies back to its takeoff point.
Land Immediately: If GPS is also jammed, the drone cannot navigate home and will typically descend vertically where it hovers.
Key Characteristics of RF Jamming:
Mechanism: Denial of Service (Noise Overload)
Precision: Low to Medium (Broadband jammers affect everything in the band, including Wi-Fi and Bluetooth).
Outcome: Drone loses control and/or positional awareness. It either leaves the area (RTH) or lands.
GPS Spoofing is a far more sophisticated and surgical form of electronic warfare. Instead of simply drowning out the real GPS signal with noise, a spoofer transmits a counterfeit GPS signal that is slightly stronger than the authentic satellite signals. This fake signal contains false coordinates and timing data.
Because GPS receivers are designed to lock onto the strongest signal available, the drone (or any GPS device in the area) will accept this counterfeit signal as truth. Spoofing is akin to replacing a ship’s navigation charts with an identical-looking map that has the lighthouse marked in the wrong place.
How the Drone Reacts to GPS Spoofing:
The drone does not know it is being attacked. It believes its navigation system is working perfectly. The attacker can subtly or dramatically alter the drone’s perceived location.
Subtle Drift: The attacker shifts the coordinates slowly over time, causing the drone to “drift” off course without triggering any alarms.
Forced Landing: The attacker spoofs a signal indicating the drone has reached its “home” point, causing it to land immediately at a location chosen by the defender.
Altitude Manipulation: The attacker can falsify altitude data, causing the drone to fly into the ground or a building if relying solely on GPS for terrain avoidance.
Key Characteristics of GPS Spoofing:
Mechanism: Impersonation / Deception (Signal Substitution)
Precision: High (Can target a specific area or single drone with directed antennas).
Outcome: Attacker gains control over the drone’s navigation without the pilot knowing.
| Feature | RF Jamming | GPS Spoofing |
|---|---|---|
| Method | High-power noise transmission | Transmission of counterfeit navigation signals |
| Effect on Drone | Loss of signal / Failsafe triggered | Drone follows false location data |
| Technical Complexity | Low to Moderate | High (Requires signal simulation & sync) |
| Collateral Damage | High. Affects Wi-Fi, Bluetooth, and all GPS in range. | Variable. Can be tightly controlled with beamforming. |
| Legality (Civilian Use) | Illegal in most jurisdictions. | Highly Illegal / Classified. Often restricted to state actors. |
| Predictability of Outcome | Predictable (RTH or Land) | Unpredictable (Depends on drone firmware response to sudden position jumps) |
| Best Use Case | Perimeter defense / Denying area access | Hostile takeover / Redirecting drone away from a moving VIP convoy |
The answer depends entirely on the mission objective and the legal authority to operate.
Choose RF Jamming When:
Simplicity and Reliability are paramount. You want the drone to simply “go away” (Return-to-Home).
You are operating in a military exclusion zone where collateral interference with local Wi-Fi is an acceptable trade-off for airspace security.
You are defending a fixed, static perimeter.
Choose GPS Spoofing When:
Stealth is required. The drone pilot may not realize their drone is being manipulated; they only see the video feed drift or landing sequence activate without a “Signal Lost” warning.
You need to capture the drone intact. Because the drone thinks it is landing safely at home, it will descend gently, allowing for forensic analysis of the payload or flight logs.
You need to move the threat. Spoofing can guide a drone to a designated “safe crash zone” or “diversion pond” away from crowds.
It is vital to reiterate that both RF Jamming and GPS Spoofing are illegal for civilian or commercial use in virtually every country worldwide. These activities constitute intentional interference with licensed radio communications and aviation navigation systems.
RF Jamming is a violation of telecommunications laws (e.g., FCC Part 15 in the US, R&TTE in EU).
GPS Spoofing is considered a threat to aviation safety and is often prosecuted under anti-terrorism or computer fraud statutes.
Only authorized government agencies (military, federal law enforcement, and national security services) are permitted to use these techniques, and even then, usually under strict coordination with aviation authorities.
While both RF Jamming and GPS Spoofing fall under the umbrella of “electronic attack,” they are as different as a sledgehammer and a lockpick.
RF Jamming is the sledgehammer: loud, powerful, and effective at clearing an area, but with significant collateral impact.
GPS Spoofing is the lockpick: quiet, precise, and capable of manipulating the target without detection, but requiring exceptional technical skill and legal clearance.
As drone technology advances and swarms become more autonomous (relying less on RF links and more on onboard AI), the relevance of GPS Spoofing will likely increase, while RF Jamming will remain the workhorse for high-intensity electronic warfare. Understanding the difference is the first step toward building a layered, resilient airspace defense architecture.
86-13920737097
AddBuilding 2, Honggao Industrial Park, Bao’an District, Shenzhen, China.
E-mailjackyjingtj@gmail.com
Copyright @ 2026 BNT Jammer
Copyright @ 2026 BNT Jammer
Copyright @ 2026 BNT Jammer